— September 10, 2019

- According to the 2019 Verizon Data Breach Investigation Report, manufacturing has been experiencing an increase in financially motivated breaches in the past couple of years, whereby most breaches involve Phishing and the use of stolen credentials.
- 50% of manufacturers report experiencing a breach over the last 12 months, 11% of which were severe according to Sikich’s 5th Manufacturing and Distribution Survey, 2019.
- Manufacturing’s most commonly data compromised includes credentials (49%), internal operations data (41%), and company secrets (36%) according to the 2019 Verizon Data Breach Investigation Report.
- Manufacturers’ supply chains and logistics partners targeted by ransomware which have either had to cease operations temporarily to restore operations from backup or have chosen to pay the ransom include Aebi Schmidt, ASCO Industries, and COSCO Shipping Lines.
Small Suppliers Are A Favorite Target, Ask A.P. Møller-Maersk
Supply chains are renowned for how unsecured and porous they are multiple layers deep. That’s because manufacturers often only password-protect administrator access privileges for trusted versus untrusted domains at the operating system level of Windows NT Server, haven’t implemented multi-factor authentication (MFA), and apply a trust but verify mindset only for their top suppliers. Many manufacturers don’t define, and much less enforce, supplier security past the first tier of their supply chains, leaving the most vulnerable attack vectors unprotected.
It’s the smaller suppliers that hackers exploit to bring down many of the world’s largest manufacturing companies. An example of this is how an accounting software package from a small supplier, Linkos Group, was infected with a powerful ransomware agent, NotPetya, bringing one of the world’s leading shipping providers, A.P. Møller-Maersk, to a standstill. Linkos’ Group accounting software was first installed in the A.P. Møller-Maersk offices in Ukraine. The NotPetya ransomware was able to take control of the local office servers then propagate itself across the entire A.P. Møller-Maersk network. A.P. Møller-Maersk had to reinstall their 4,000 servers, 45,000 PCs, and 2500 applications, and the damages were between $ 250M to $ 300M. Security experts consider the ransomware attack on A.P. Møller-Maersk to be one of the most devastating cybersecurity attacks in history. The Ukraine-based group of hackers succeeded in using an accounting software update from one of A.P. Møller-Maersk’s smallest suppliers to bring down one of the world’s largest shipping networks. My recent post, How To Deal With Ransomware In A Zero Trust World explains how taking a Zero Trust Privilege approach minimizes the risk of falling victim to ransomware attacks. Ultimately, treating identity as the new security perimeter needs to be how supply chains are secured. The following geographical analysis of the attack was provided by CargoSmart, showing how quickly NotPetya ransomware can spread through a global network:
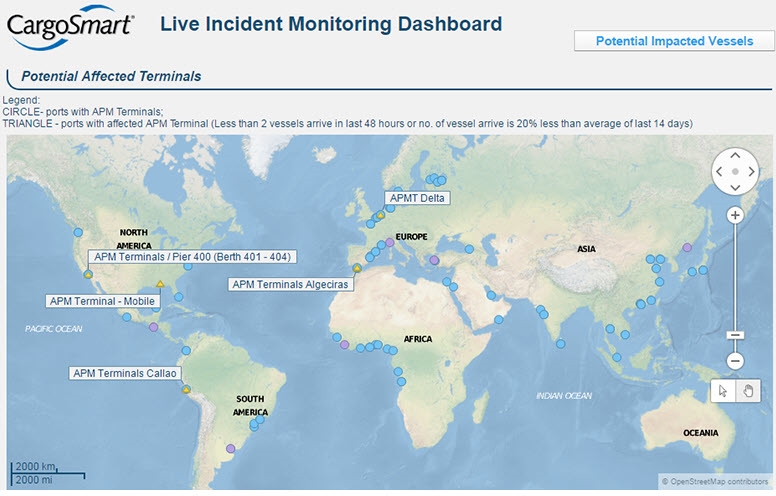
CargoSmart provided a Vessel Monitoring Dashboard to monitor vessels during this time of recovery from the cyber attack.
Supply Chains Need To Treat Every Supplier In Their Network As A New Security Perimeter
The more integrated a supply chain, the more the potential for breaches and ransomware attacks. And in supply chains that rely on privileged access credentials, it’s a certainty that hackers outside the organization and even those inside will use compromised credentials for financial gain or disrupt operations. Treating every supplier and their integration points in the network as a new security perimeter is critical if manufacturers want to be able to maintain operations in an era of accelerating cybersecurity threats.
Taking a Zero Trust Privilege approach to securing privileged access credentials will help alleviate the leading cause of breaches in manufacturing today, which is privileged access abuse. By taking a “never trust, always verify, and enforce least privilege” approach, manufacturers can protect the “keys to the kingdom,” which are the credentials hackers exploit to take control over an entire supply chain network.
Instead of relying on trust but verify or trusted versus untrusted domains at the operating system level, manufacturers need to have a consistent security strategy that scales from their largest to smallest suppliers. Zero Trust Privilege could have saved A.P. Møller-Maersk from being crippled by a ransomware attack by making it a prerequisite that every supplier must have ZTP-based security guardrails in place to do business with them.
Conclusion
Among the most porous and easily compromised areas of manufacturing, supply chains are the lifeblood of any production business, yet also the most vulnerable. As hackers become more brazen in their ransomware attempts with manufacturers and privileged access credentials are increasingly sold on the Dark Web, manufacturers need a sense of urgency to combat these threats. Taking a Zero Trust approach to securing their supply chains and operations, helps manufacturers to implement least privilege access based on verifying who is requesting access, the context of the request, and the risk of the access environment. By implementing least privilege access, manufacturers can minimize the attack surface, improve audit and compliance visibility, and reduce risk, complexity, and costs for the modern, hybrid manufacturing enterprise.
Business & Finance Articles on Business 2 Community
(76)
Report Post